OfficialUSA Opt Out Guide To Protect Your Personal Information
This OfficialUSA opt out guide will help you protect your personal details so they don’t fall into the wrong hands.
Protecting your online privacy and personal information is crucial in the digital age. OfficialUSA.com is a site that shares public records and personal data, which can be a privacy risk. This guide will help you opt out of having your listing on the OfficialUSA.com data broker site, ensuring your information remains private.
We’ll also discuss the risks of having your data on a people search website. Additionally, we’ll help you practice online safety by suggesting steps like reviewing your presence, securing your data, being cautious with online transactions, using two-factor authentication, and keeping software updated for a safer online experience.
At Internet Privacy, we offer monitoring and removal of your personal information so you can better protect your identity. Contact us today at 866-349-0130 to learn more.
What is OfficialUSA.com and What Information Does it Provide?
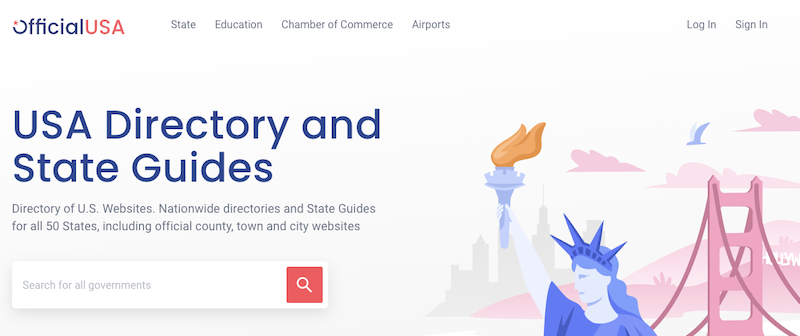
OfficialUSA compiles personal information from various sources, making accessing details like your full name, home address, phone number and other personal details extremely easy. This convenience raises privacy concerns and potential risks, as the site doesn’t verify the accuracy of the information it provides. Leaving your private data online on OfficialUSA.com can harm your reputation and even lead to identity theft.
To protect your privacy and reduce these risks, it’s advisable to request data removal. We’ll outline the required data removal steps to follow so that your information is no longer in the website’s database.
Why Opt Out of OfficialUSA.com?
Opting out of OfficialUSA.com is crucial to protecting your privacy, maintaining control over your online presence, and keeping your personal information confidential. It also safeguards your data from unauthorized access and reduces identity theft risk.
Additionally, removing your info from the people search website prevents it from appearing in search engine results, reducing spam and solicitations. Opting out ensures your data stays confidential, shielding you from other data brokers’ invasive practices.
Privacy Concerns and Risks of Leaving Your Information on OfficialUSA.com

Leaving your data on sites like OfficialUSA.com poses serious privacy and security risks. Your personal details, including your full name, financial information and property details, can be easily accessed, leading to identity theft and fraud. You’ll also face unwanted spam emails and telemarketing calls, disrupting your daily life.
Third-party companies may also access and use your data without consent, compromising your privacy and control over your information. To protect yourself, remove information from OfficialUSA using the following guide.
Additionally, safeguard your online presence by regularly reviewing your digital footprint, being cautious with online transactions, using two-factor authentication, and keeping your software updated. Taking these steps is essential to protect your personal and financial well-being.
Our internet privacy experts will protect you from identity theft, phishing attacks and other online threats. Call us at 866-349-0130 for more information.
Step-by-Step Guide to Opting Out of OfficialUSA.com
Looking to safeguard your personal information from OfficialUSA.com? Look no further! This step-by-step guide will walk you through opting out, ensuring your data remains secure. We’ll cover everything from discovering your information on OfficialUSA.com to submitting the opt-out request. Let’s get started on reclaiming your privacy and taking control of your data.
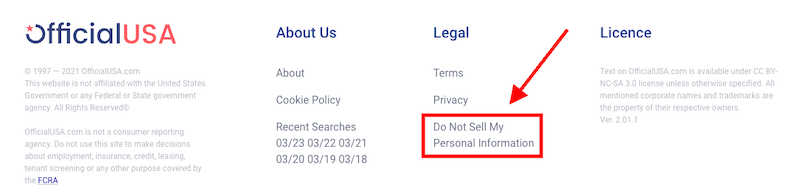
Step 1: Go to the opt-out page
Start on the OfficialUSA home page here. Scroll to the bottom of the page. In the footer, click the Do Not Sell My Personal Information link.
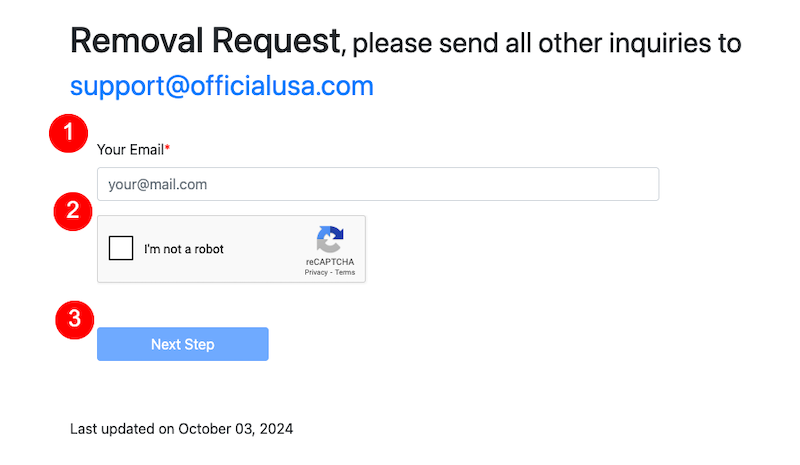
Step 2: Enter your email address and proceed with the opt-out form
After clicking that link, you’ll be directed to the first page of the opt-out form. Enter your email address in the designated space, click the captcha box, and then click the Next Step button.
Step 3: Find your information on OfficialUSA
In this step, you’re going to find the information that you want OfficialUSA to remove. Enter your first and last name, then click Find Person.
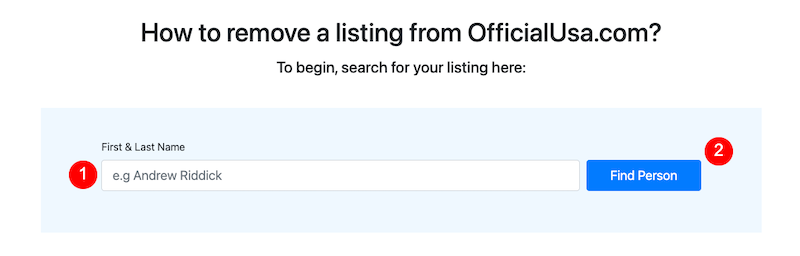
If no results are found, try alternative names, like your maiden name, for example, as well as common misspellings of your name.
Step 4: Select your data to remove it
If you’re able to find your information on the OfficialUSA website, click the Open Circle to the left of it, then click the Remove button.
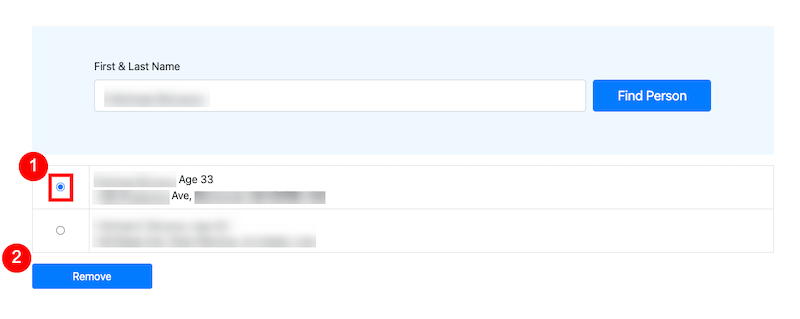
If there are multiple records with the same name or information, review them both to make sure you’re selecting the right one. It’s possible that there will be more than one result with your information, and you’ll need to go through these steps again to remove additional instances of your profile being on the site.
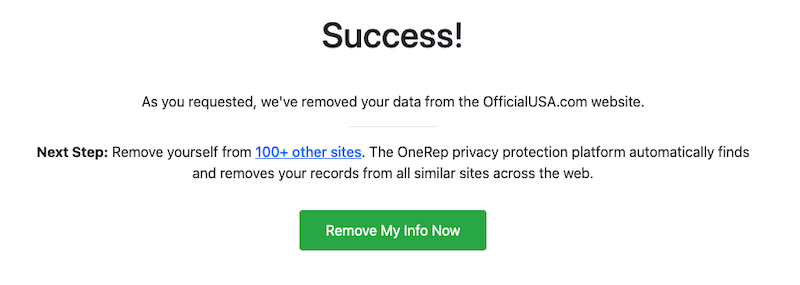
Step 5: Wait for the “Success” message
Once you’ve submitted the removal request, you’ll be redirected to a “Success!” confirmation page, which confirms that your information will be removed from the OfficialUSA site.
We work on behalf of our clients to monitor their online data and remove personal information from the internet. Give us a call at 866-349-0130 to learn more.
5 Important Tips for Maximizing Your Online Safety
Next, let’s go over five must-know ways to stay safe online beyond following the opt out procedure for any data broker site you need to remove information from.
Regularly Review Your Online Presence
Regularly reviewing your online presence is crucial for privacy and security:
- Update passwords to prevent unauthorized access and perform a name-based Google search to see your online information.
- Check and adjust social media privacy settings to control who views your private data.
- Monitor credit reports and financial accounts for suspicious activity, which can signal identity theft.
- Consider using an identity theft protection service for continuous monitoring and threat detection.
These practices help you to actively manage and protect your personal information, reducing the risk of someone misusing it.
Secure Your Personal Information
Securing your personal information is essential to protect against online privacy breaches and identity theft. Take proactive steps, including the following:
- Using strong, unique passwords
- Enabling two-factor authentication
- Sharing personal information only on secure platforms
- Regularly reviewing and adjusting privacy settings
- Keeping your devices and software updated with security patches
These actions significantly reduce the risk of unauthorized access to your data. Remember, online safety is an ongoing process that requires vigilance in the face of evolving privacy threats.
Be Cautious with Online Transactions

Protecting your personal and financial information during online transactions is essential:
- Verify website security by looking for “https” and a padlock icon
- Use secure payment methods like PayPal
- Be cautious of phishing attempts
- Keep software updated
- Monitor bank statements for unauthorized charges
- Use strong, unique passwords
Following these precautions safeguards you from online fraud and ensures a secure online transaction experience.
Set Up Two-Factor Authentication
Enhance your online security with these two-factor authentication (2FA) tips:
- Enable 2FA in your account settings for all your accounts
- Choose a reliable method like SMS codes or authenticator apps
- Keep backup codes secure
- Transfer 2FA settings to new devices
Remember, 2FA is an extra layer of security but not foolproof, so continue using strong, unique passwords for added protection.
Keep Software and Devices Updated
To enhance online safety, keeping your software and devices up to date is crucial. It’s smart to enable automatic updates for your operating system and essential applications, which ensures you receive the latest security patches without manual intervention.
If automatic updates aren’t available or enabled, make it a routine to check for updates regularly, covering your OS, antivirus software, web browser, and other critical programs. Don’t forget to check and update firmware for devices such as routers and smart TVs, too, as these updates often contain important security patches.
Additionally, always download software and applications from trusted sources, like official websites or reputable app stores, to reduce the risk of downloading malicious content.
Lastly, maintain regular data backups to safeguard your important information. If an update causes any issues, this will allow you to recover and minimize potential data loss quickly.
Keeping software and devices up to date is fundamental to ensuring a secure online experience by mitigating vulnerabilities and cyber threats.
Speak With an Internet Privacy Expert
At InternetPrivacy.com, we offer “remove my info” services to get rid of your personal information and help you protect your identity and the identities of your loved ones online. Our data removal services include deep web scans, ongoing monitoring and detailed reporting.
You deserve to protect your personal and sensitive information online. To keep it from getting into the wrong hands, you can trust our decade-plus of experience defending individuals and businesses on the internet.
Do you need help with data removal? Get started for free with a quick personal data scan.





