Internet Privacy uses advanced search engine marketing tools
to assure complete and accurate information removal.

We scour the Internet for any exposed data, including the names of your relatives and children. We conduct searches under multiple name variations to find as many records as possible.

Our internet privacy solutions make it easy for you to secure your digital identity. We ensure your personal information is protected at all times, and we help you remove yourself from data collection sites.
We periodically check the status of all removals and purge any new records found. And since the Internet never sleeps, we continuously search for new sources of personal information that require removal.

You’ll receive regular reports on your privacy status and any outstanding threats. If any new records become associated with you, we send you an alert.

Your privacy is personal, which is why we want to provide you a human-touch. You’ll receive access to a privacy support representative who is available for questions, concerns, or any other requests you may have regarding your privacy account.

InternetPrivacy.com is the software sister company of NetReputation.com, North America’s leading online reputation specialists and Inc 500 company. Internet Privacy has taken over a decade of experience managing, monitoring, and safeguarding online privacy concerns for both individuals and businesses and put it into a software that provides industry-leading protection for you and your family.
Protect your personal and private information online today, and have our team remove any unwanted or negative content.
Every second, over 70 people-search sites publish and sell your personal information to third parties for next to nothing.

Hackers increasingly turn to phishing attacks to try to extract passwords, credit card information, and other sensitive data from their targets. Active Internet Privacy Protection makes this much harder to do.

Personal information is easy to find on the Internet. Directories, reverse look-ups, and many other services make it their business to collect and sell vast troves.

Stalkers and disgruntled acquaintances increasingly turn to the Internet to find addresses, phone numbers, and other private data about their victims.
Did you know that hackers can easily find the answers to the vast majority of common security questions online? Active Internet Privacy Protection cuts off many of these information sources, making it much harder for someone to steal your passwords and obtain your private information.

A typical InternetPrivacy audit uncovers over 300 elements of personal information across the entire internet. We remove all references of both yours and your family’s private information online.
Try for Free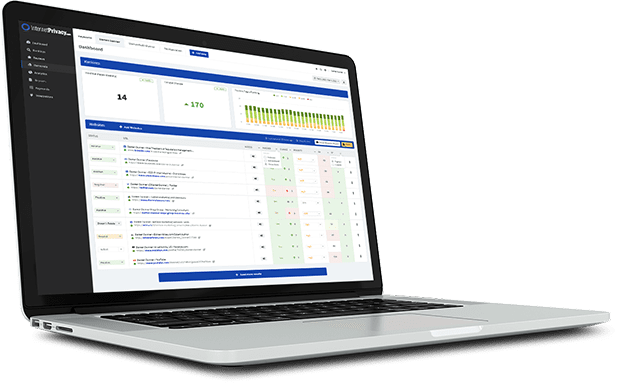
There are 100+ people-search sites online where your information may be exposed. We scan all these online databases & remove your information wherever it is found.
Start Removal Process

Every click, search, and website visit leaves a digital trail. This trail, known as browser history, is more than just
Read More
Neighborhood watch apps promise safer streets, stronger communities, and real-time safety alerts. But as these platforms expand into everything from
Read More
Every time you check the weather on your phone, a hidden exchange begins. Your device doesn’t just fetch a forecast—it
Read More